MQTT Concept: The Universal Language of Modern IoT (2026 Guide)
Introduction
Regardless of the application type, seamless information exchange between two points is a pivotal operational step. IoT or Internet of Things application development is on the rise and is not free from this crucial requirement. That’s where Message Queue Telemetry Protocol comes into picture.
Often referred to as MQTT, it is a reliable messaging protocol advancing conversations for IoT solutions smoothly. In this article, we will help you gain command over all information related to it.

What is MQTT? (Introduction to the Protocol)
At its core, MQTT (Message Queuing Telemetry Transport) represents a minimalist approach to machine-to-machine (M2M) communication. It isn't just a protocol; it's a strategic solution for moving data across fragile, bandwidth-starved, or high-latency networks.
While initially engineered for industrial SCADA systems at the turn of the century, the 2026 landscape sees MQTT powering everything from hyper-scalable cloud architectures to decentralized edge computing. Its brilliance lies in its "silent" nature consuming negligible energy while ensuring data reaches its destination.
Why is the MQTT Protocol Important for IoT?
Understanding the Internet of Things (IoT) means realizing that it's a rapidly evolving technology domain where a diverse range of gadgets, from the everyday smartphone to complex industrial machinery, are connected via the internet. This interconnectedness permits the instant gathering and scrutiny of data, resulting in improved effectiveness and productivity. Nonetheless, with the massive surge of data production by these gadgets, a strong and efficient mode of communication is required. This is precisely where MQTT (Message Queuing Telemetry Transport) comes in.
MQTT: A Key Player in IoT Communication
View MQTT as a lean, publish-subscribe networking protocol that facilitates the shuttle of messages between devices. It's engineered particularly for gadgets with restrictions and for networks characterized by decreased bandwidth, increased latency, or lack of reliability. MQTT guarantees dependable message transportation at distinct Quality of Service (QoS) degrees, solidifying it as a top choice for IoT usage.
MQTT wears many hats in the sphere of IoT. Acting as an intermediary between devices and the internet, MQTT facilitates seamless networking. Additionally, it ensures efficient and secure transmission of data, even amidst network difficulties.
MQTT & IoT: A Match Made in Tech Heaven
Several reasons make MQTT an exceptional protocol for IoT usage:
- Efficiency: MQTT boasts a design that optimizes both bandwidth consumption and computational resources, a major advantage for IoT gadgets often characterized by limited processing capability and memory.
- Quality of Service: MQTT presents a three-tier QoS system, aiding developers in striking a balance between data delivery assurance and network bandwidth use.
- Security: MQTT utilizes Transport Layer Security (TLS) to uphold secure transmission, safeguarding data from unwarranted access.
- Scalability: MQTT's ability to sustain a multitude of connections makes it fit for widespread IoT deployments.
- Economical: MQTT operates on a publish-subscribe model which economises network bandwidth by circulating data only when necessary.
Witness MQTT in Action: IoT Applications
MQTT is employed across an array of IoT uses. For instance, in automated homes, MQTT can regulate and oversee gadgets like lighting, temperature control, and security systems. Within the Industrial IoT, MQTT could be employed to keep track of machinery and equipment, supplying instant data on their operation and maintenance demand.
Imagine an automated home setup where different gadgets such as lights, temperature control, and security systems need to interact. MQTT functions as the communication protocol that facilitates these devices to exchange messages. For example, a temperature control can dispatch a message to an MQTT broker if the temperature descends below a predetermined value. The broker can then channel this message to all subscribed gadgets, such as the heating system, which can then respond accordingly.
# An example MQTT message
client.publish("autohome/temperaturecontrol", "temp: 18")
In an Industrial IoT setup, MQTT could be employed to track machinery and equipment. Sensors attached to non-negligible assets dispatch data to an MQTT broker. The broker then channels this information to all suitable gadgets. This live data can be exploited to oversee performance, predict upkeep requirements, and detect irregularities.
# An example MQTT message
client.publish("industrial/asset1", "vibration level: 3.2")
MQTT & IoT: The Voyage Continues
As the IoT evolves, MQTT's role fortifies. With its efficient design, robust QoS choices, and support for secure transmission, MQTT is equipped to manage the communication demands of the IoT, ranging from minor home automation systems to major industrial deployments.
What is the Principle Behind MQTT? (Understanding the Architecture)
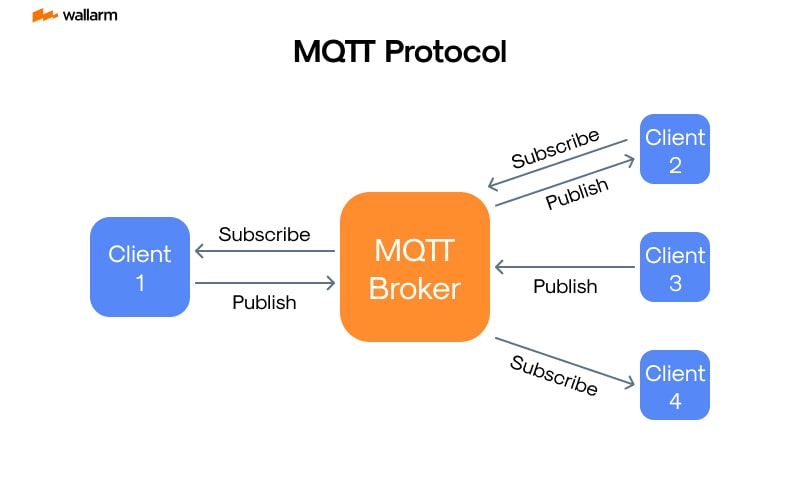
MQTT flips the script on the standard Request/Response cycle used by the web. It utilizes a triadic Pub/Sub pattern that provides three essential layers of isolation:
- Spatial Independence: Components function without direct IP-to-IP awareness.
- Temporal Fluidity: Messages can be queued and delivered even if the recipient is momentarily offline.
- Process Asynchronicity: Devices aren't forced to wait for acknowledgments, preventing system-wide bottlenecks.
Core MQTT Components: Clients, Brokers, and Topics
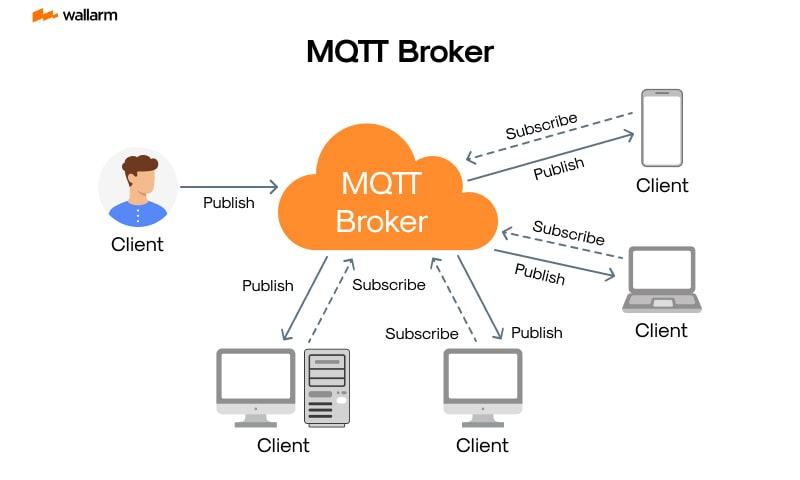
The ecosystem relies on a simple but rigid hierarchy:
- The MQTT Client: Any software-enabled hardware ranging from a C-coded microcontroller to a Python-based server capable of interfacing with the network.
- The MQTT Broker: The gatekeeper of the system. It manages session states, filters incoming streams, and ensures precise distribution.
- The MQTT Topic: A hierarchical labeling system (e.g., hq/lab_04/humidity) that acts as a virtual channel for data categorization.
How Does MQTT Protocol Work? (The Message Flow)
The lifecycle of an MQTT interaction is a four-step choreography:
- Handshake: The client establishes a persistent connection via a CONNECT packet.
- Interest Declaration: The client registers its interest in specific data via a SUBSCRIBE request.
- Data Ingestion: An uplink device pushes information via a PUBLISH event.
- Targeted Delivery: The broker intelligently broadcasts the payload only to the relevant authenticated subscribers.
MQTT Quality of Service (QoS) Levels
Celebrated as the crux of machine-based dialogue, the advanced protocol MQTT (Message Queuing Telemetry Transport) leverages an ingenious model of data interchange that is universally known as the "publish/subscribe model". Its capabilities get further magnified with the introduction of an intricate layered framework known as Quality of Service (QoS) which is catered to assure the dependability of data transfer.
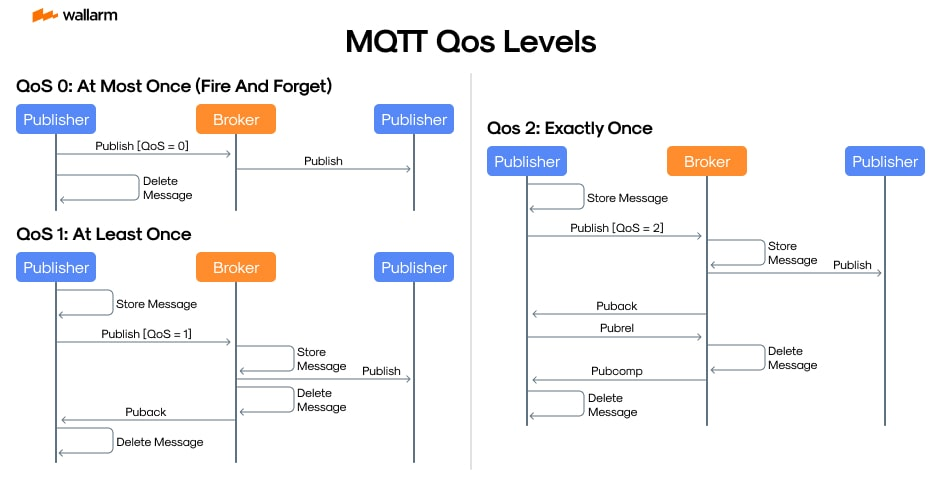
Exploring the Modus Operandi of MQTT QoS
The MQTT's QoS structure is built upon three hierarchical levels that judge the surety of message delivery:
- QoS 0 – "Single Transmission": In this elementary level, every unique contact is transacted only for a single time. The originator makes no attempt to receive any validation from the recipient. This model is effective when the sporadic loss of messages is trivial.
- QoS 1 – "One or More": The intermediary layer ensures the arrival of each sent message to the associated machine at the bare minimum once, and potentially multiple instances. The sender sustains the message till an approval confirmation is obtained. In case of absence of response within a particular time frame, the message is retransmitted, ensuring no lost messages at the expense of potential double-ups.
- QoS 2 – "Once and Only Once": This apex layer assures the single-time transfer of a message. This is facilitated via a procedure of four steps of interchange between the originator and receiver, effectively nullifying double-ups or misplacements. This is a dovetail for ensuring data accuracy and uniformity.
The Reinforcement of Data Transfer by QoS Levels
The selection of QoS level should be coherent with your app necessities. For instance, if you're working with sensor data, where mishap of information is immaterial, QoS 0 is adequate. Conversely, where precision is of utmost importance, QoS 2 is the supreme choice.
The messaging precision not just affects the efficiency of MQTT's network but also influences its operational requisites. More stringent QoS levels might require more digital resources and bandwidth due to escalated storage needs and control message generation. Hence, the harmony of system reliability and peak performance is crucial in deciding QoS levels.
Synoptic Representation of MQTT QoS Levels
QoS Levels Comparison Table
| QoS Level | Consistency in Delivery | Possibility of Message Loss | Chances of Duplication | Bandwidth Necessity | Ideal Utilization |
|---|---|---|---|---|---|
| 0 | One Occurrence | Possible | Improbable | Minimal | Basic Data Transfer |
| 1 | One or More | No Possibility of Loss | Potential Double-ups | Medium | Scenarios Accepting Double-ups |
| 2 | Single Instance | No Loss | No Duplication | Substantial | Critical Use Cases Requiring Precision |
Implementing MQTT QoS in App Development
While dispatching a message via MQTT, one can define the QoS level in the input panel. As an example, if we take into account a Python script leveraging the Paho MQTT library to dispatch a message using QoS 1, the code would appear like this:
import paho.mqtt.client as mqtt_module
mqtt_client_architecture = mqtt_module.Client()
mqtt_client_architecture.connect("mqtt.example.com", 1883, 60)
mqtt_client_architecture.publish("topic", "message", qos=1)
mqtt_client_architecture.disconnect()
In this code snippet, the publish method encompasses three parameters: topic, message, and predilected QoS level.
The diverse levels of MQTT's Quality of Service curate supple and certain message rove within miscellaneous Internet of Things (IoT) applications. By discerning and judiciously using these levels, it's plausible to engineer robust, high-productivity IoT infrastructures leveraging MQTT.
Is MQTT Secure? (Security Best Practices in 2026)
In an era of rising cyber threats, MQTT security must be multi-layered. At Wallarm, we recommend a "Zero Trust" approach to IoT:
- Encrypted Tunnels: Mandating TLS 1.3 on port 8883 to eliminate man-in-the-middle risks.
- Granular Identity: Moving beyond simple passwords to X.509 client certificates.
- Content Validation: Inspecting payloads for injection attacks that might target the broker or backend databases.
MQTT vs HTTP: A Comparative Analysis
MQTT vs HTTP Comparison Table
| Metric | MQTT (Event-Driven) | HTTP (Stateful/REST) |
|---|---|---|
| Philosophy | "Push" notifications | "Pull" requests |
| Payload Size | Minimalist (Binary) | Bulky (JSON/XML) |
| Power Drain | Ultra-Low (Sleep-friendly) | High (Active polling) |
| Connectivity | Always-on / Long-lived | Stateless / Short-lived |
In today's digitally-oriented society, the seamless management of data flow is of utmost importance. In this respect, two significant players emerge, MQTT and HTTP, each bringing its own set of benefits in the realm of data communication.
Understanding MQTT:
Conceived predominantly for networks characterized by sporadic connections, high latency, and narrowed bandwidth, MQTT excels in the realm of the Internet of Things (IoT), courtesy of its minimal power usage and restricted data packet size.
Key Highlights of MQTT:
- The size of MQTT messages is significantly limited, helping to save valuable network bandwidth.
- Leaning on a unique publish-subscribe model, MQTT opens up opportunities for one-to-many communication.
- A range of Quality of Service (QoS) options featured by MQTT ensures consistent message delivery even with unstable network conditions.
- The ability to broadcast a final message in the event of an unexpected disconnection is a distinctive feature of MQTT, known as 'Last Will and Testament'.
Understanding HTTP:
HTTP, the linchpin in online data transfers, facilitates the movement of data over the internet.
Key Highlights of HTTP:
- The straightforward request-response model of HTTP simplifies its utilization.
- The mechanism of HTTP operates on a stateless basis, with each interaction between server and client treated as distinctive.
- The capability of HTTP to handle all types of data, given suitable client and server compatibility, showcases its flexibility.
- Universal acceptance and implementation across all digital devices echo HTTP's versatility.
How do MQTT and HTTP Stand Against Each Other?
Efficiency and Bandwidth Consumption
When it comes to data transfer efficiency, MQTT has the upper hand over HTTP, thanks to the compactness of MQTT messages. Conversely, HTTP has more comprehensive headers leading to larger amounts of data transmission.
Messaging Protocols
The strength of MQTT lies in its publish-subscribe model, as opposed to HTTP's request-response model. MQTT's model promotes convenient one-to-many interaction, a boon for IoT scenarios with several devices involved. The HTTP model aligns well with standard web applications.
Quality Assurance
MQTT provides three tiers of Quality of Service (QoS), ensuring dependable message delivery, something that HTTP cannot guarantee.
Connection Maintenance
In MQTT, a continuous connection state between the server and the client facilitates instant communication as there's no need to reestablish a connection for each message. In comparison, HTTP treats each request as a new connection.
Suitability for Applications
Owing to its lean structure, reduced power usage, and efficient data handling, MQTT thrives in IoT applications and is used extensively in industrial IoT solutions, smart home appliances, and vehicle telematics.
HTTP, on the other hand, with its wider acceptance and ability to adapt, fares well with web-based applications. Its uses range from web browsing and data streaming to file transfers.
In conclusion, the choice between MQTT and HTTP hinges on the specific requirements of the application. MQTT shines in IoT related instances, where efficiency, less power consumption, and assured data delivery take precedence. HTTP, with its wide usage and versatility, comes into play for traditional web applications.
How do MQTT and HTTP Stand Against Each Other?
The choice is context-dependent. HTTP remains the standard for web API interaction and large file transfers. However, for real-time telemetry and battery-constrained remote assets, MQTT is the undisputed victor due to its 10x reduction in header overhead.
Top MQTT Trends in 2026
- MQTT over QUIC: The transition from TCP to QUIC allows for near-zero latency reconnections in 5G environments.
- AIoT Pipelines: High-velocity MQTT streams now feed directly into real-time inference engines for predictive maintenance.
- Sparkplug B & UNS: Standardizing industrial data into a Unified Namespace to bridge the gap between the factory floor and the boardroom.
How Wallarm Safeguards Your MQTT Ecosystem
As the adoption of MQTT 5.0 and Industry 4.0 accelerates, the protocol has become a prime target for sophisticated cyber-attacks. While MQTT provides basic encryption, it often lacks the deep packet inspection required to stop advanced threats. This is where Wallarm bridges the gap between connectivity and ironclad security.
Wallarm’s Integrated AppDomain and API Security platform provides a dedicated shield for your IoT infrastructure through:
- Attack Detection & Mitigation: Wallarm identifies and blocks common MQTT exploits, such as Topic Flooding (DoS) and Unauthorized Topic Injections, preventing attackers from hijacking your device communication.
- Protocol Hardening: By monitoring the traffic between clients and brokers, Wallarm ensures that only valid, authenticated messages pass through, mitigating the risk of "Malformed Packet" attacks that can crash legacy brokers.
- Discovery of Shadow IoT Endpoints: Many organizations have "ghost" MQTT brokers or forgotten IoT devices. Wallarm’s API Discovery automatically maps your entire attack surface, ensuring no MQTT endpoint remains unprotected.
- Zero-Trust Integration: Wallarm fits seamlessly into modern CI/CD pipelines, allowing security teams to enforce consistent policies across both traditional HTTP APIs and high-velocity MQTT streams.
In a world where one compromised sensor can jeopardize an entire production line, Wallarm provides the visibility and automated protection needed to scale your IoT operations with confidence.
FAQ
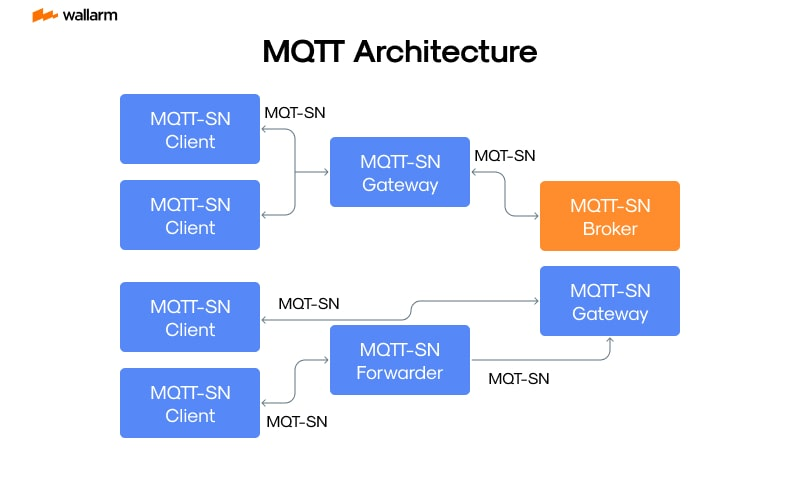
Does MQTT require TCP?
Traditionally yes, but MQTT-SN and MQTT over QUIC have introduced UDP-friendly alternatives.
What ports should I open?
Standard traffic uses 1883, but secure enterprise traffic should strictly use 8883.
How many devices can one broker handle?
With modern clustering, a single logical broker can manage hundreds of millions of simultaneous links.
References
- IoT Analytics (2025): Global IoT Connectivity Market Report.
- Eclipse Foundation: 2024-2025 Developer Trends.
- OASIS Open: Official MQTT v5.0 Documentation.
Subscribe for the latest news

















