See Wallarm's API Protection In Action


Shift left to do security right
Automated API security testing meets real-world validation test smarter, shift left, and release with confidence.
Traditional Approach




Wallarm Approach




Wallarm API Security Testing has many cool features to help DevOps teams strike the delicate balance between the security of the application and the very short release cycles.
90%
More security coverage for your API endpoints

How Does API Security Testing Work
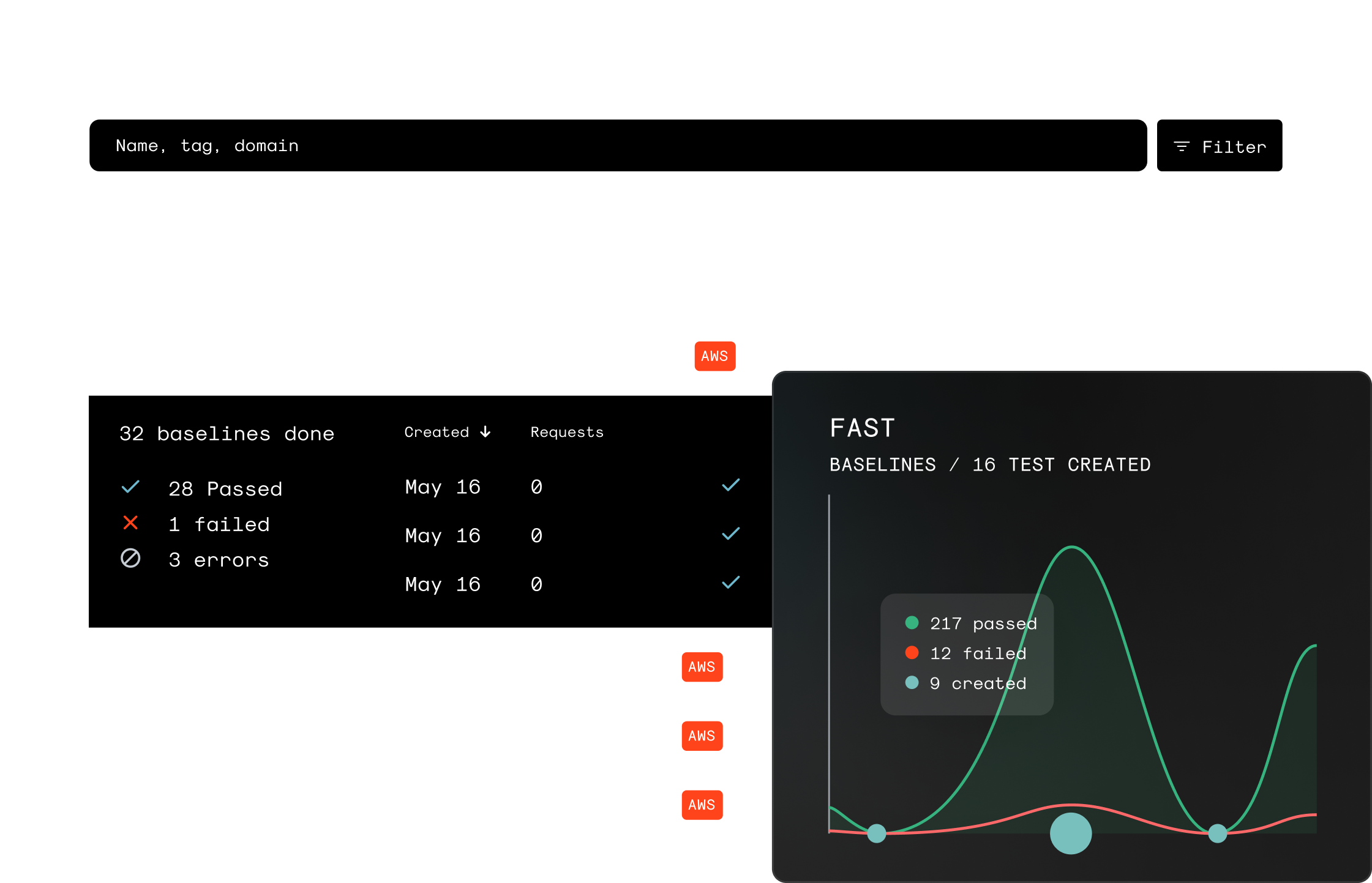
Get more from the testing you’re already doing. Wallarm automatically transforms existing functional tests into security tests in CI/CD.


A special proxy (container) captures requests to API as baselines. It then creates and runs a multitude of security checks for every build.

Use OWASP Top 10 defaults or specify your own testing policies, like types of parameters to test, payloads, or fuzzer settings.

Report security issues and anomalies to the CI pipeline and ticketing system.
Features
Setup cross-team workloads via your existing DevOps and security toolchain.

Automated Schema-based testing

Threat Replay Testing

CI/CD Integration

Compliance Ready
Integrations and Automation
Easily integrate with any CI and testing tools/frameworks already in action.

Jenkins

Gitlab
Selenium

CircleCI
Additional Resources


Ready to protect your APIs?
Wallarm helps you develop fast and stay secure.