7 Steps to Kubernetes Security
Explore seven points we have identified as absolutely essential to build a secure Kubernetes environment.
See Wallarm's API Protection In Action
Cloud native applications need more than just perimeter security. In Kubernetes clusters, Wallarm protects containerized applications, microservices, and APIs in private and public clouds. Wallarm inspects both north-south and east-west traffic to protect your cloud-native architectures.




Wallarm protects websites, APIs and microservices from OWASP API Security Top 10, bots and abuse with no manual rule configuration and ultra-low false positives.

Protects attacks against APIs

Kubernetes or container-based infrastructure

Native integration

Private data center

Out-of-band deployment

At the edge / Cloud WAAP (SaaS)
Wallarm protects websites, APIs and microservices from OWASP Top 10, bots and application abuse with no manual rule configuration and ultra-low false positives.




At the foundation of the Wallarm design ethos is privacy, flexibility and performance.
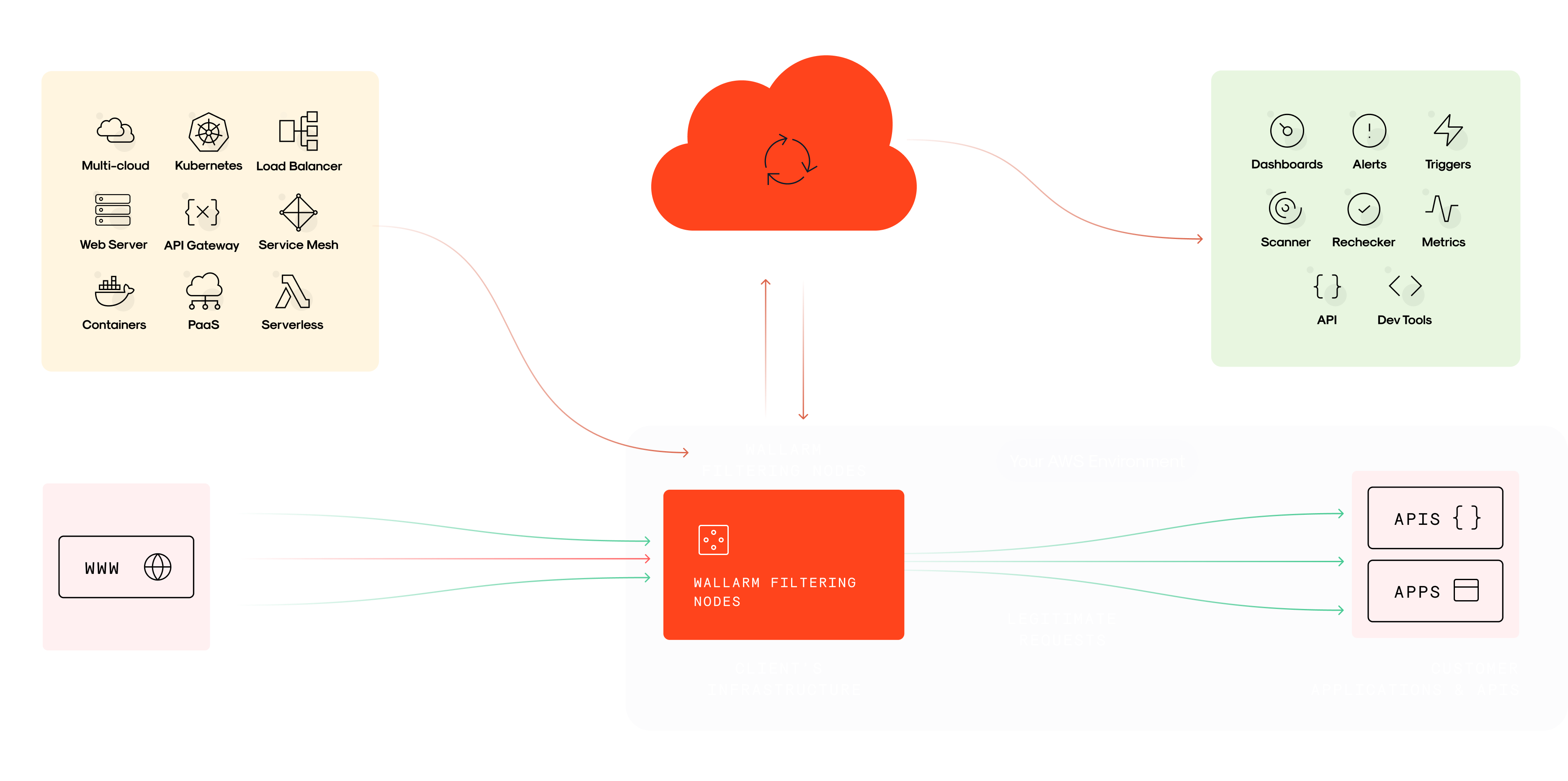
Inline deployment of our hybrid SaaS solution involves two main components: server-side software that deploys in your infrastructure within minutes and our powerful cloud-hosted analytics backend.
Privacy
Regularly monitor and review new API and web application threats & vulnerabilities 24/7 and add quick updates to the threat detection & mitigation systems – so you are staying ahead of attacks.
Flexibility
Continuously leverage the on-going data collection & analysis efforts of the Wallarm Research team for improvements in detection capabilities – so you are equipped with the best possible protection.
Performance
Read our quarterly API vulnerability report and learn why you need to set data-defensible remediation policies that engineers and executives will support.
Wallarm helps you develop fast and stay secure.